Vulnerability, Detection & Remediation
Expose What’s Been Hiding Under the Canopy
Business platforms are bursting with flows, apps, BI reports and AI agents, built by no-coders, who don’t always know where danger hides.
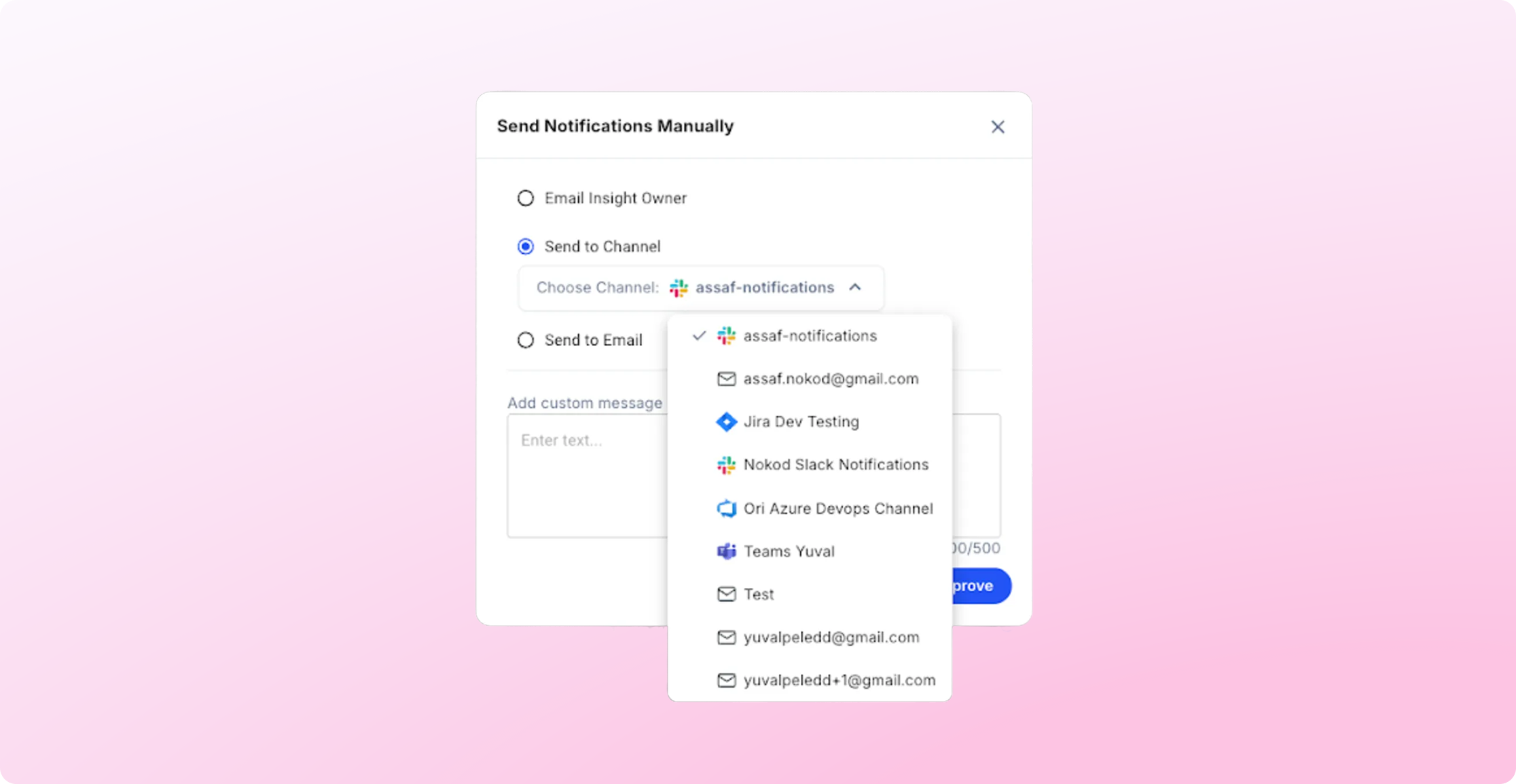
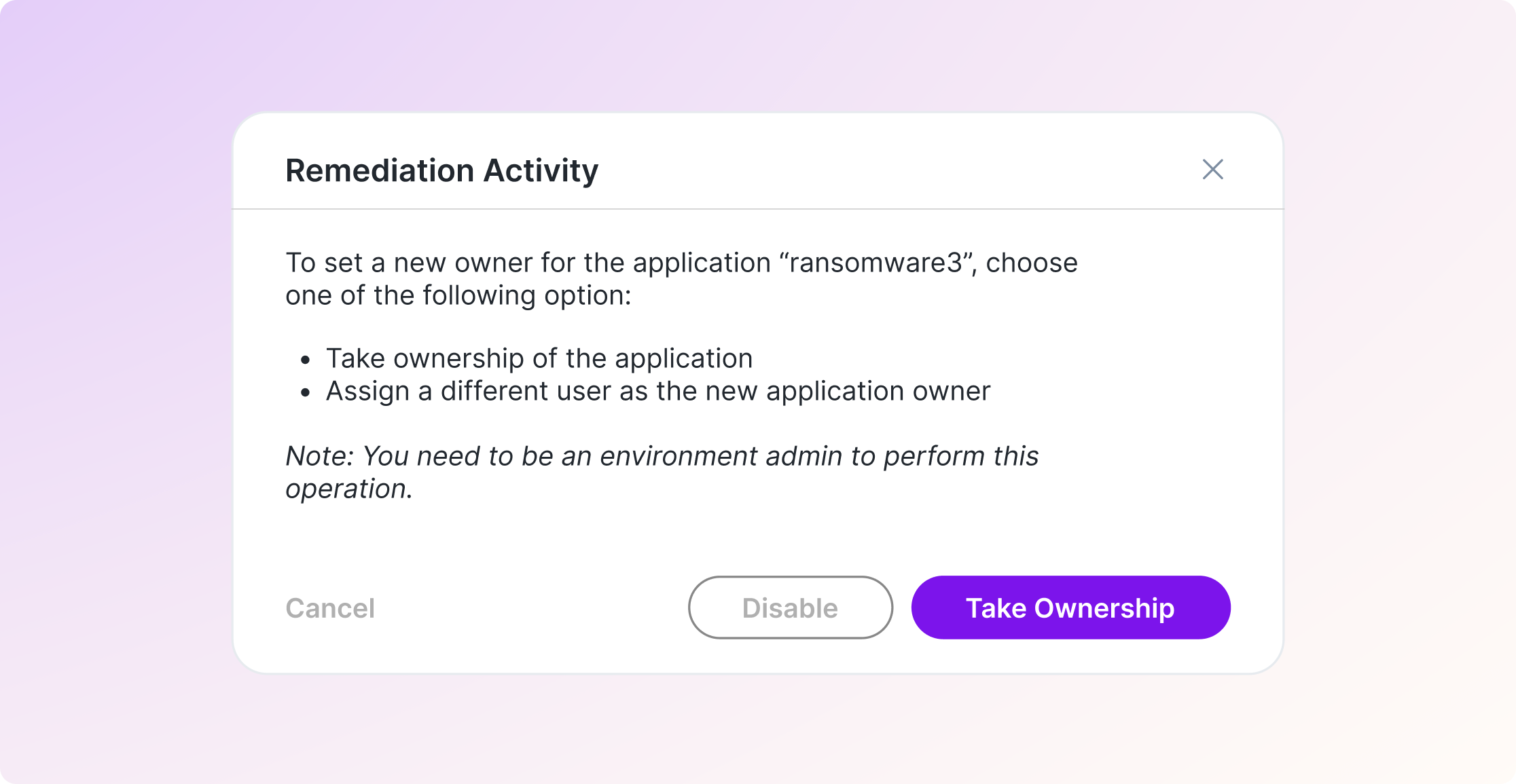
Nokod brings visibility and control to this hidden jungle, revealing what’s vulnerable, what’s risky, and how to fix it fast.
Not Everything in the Jungle Is What It Seems
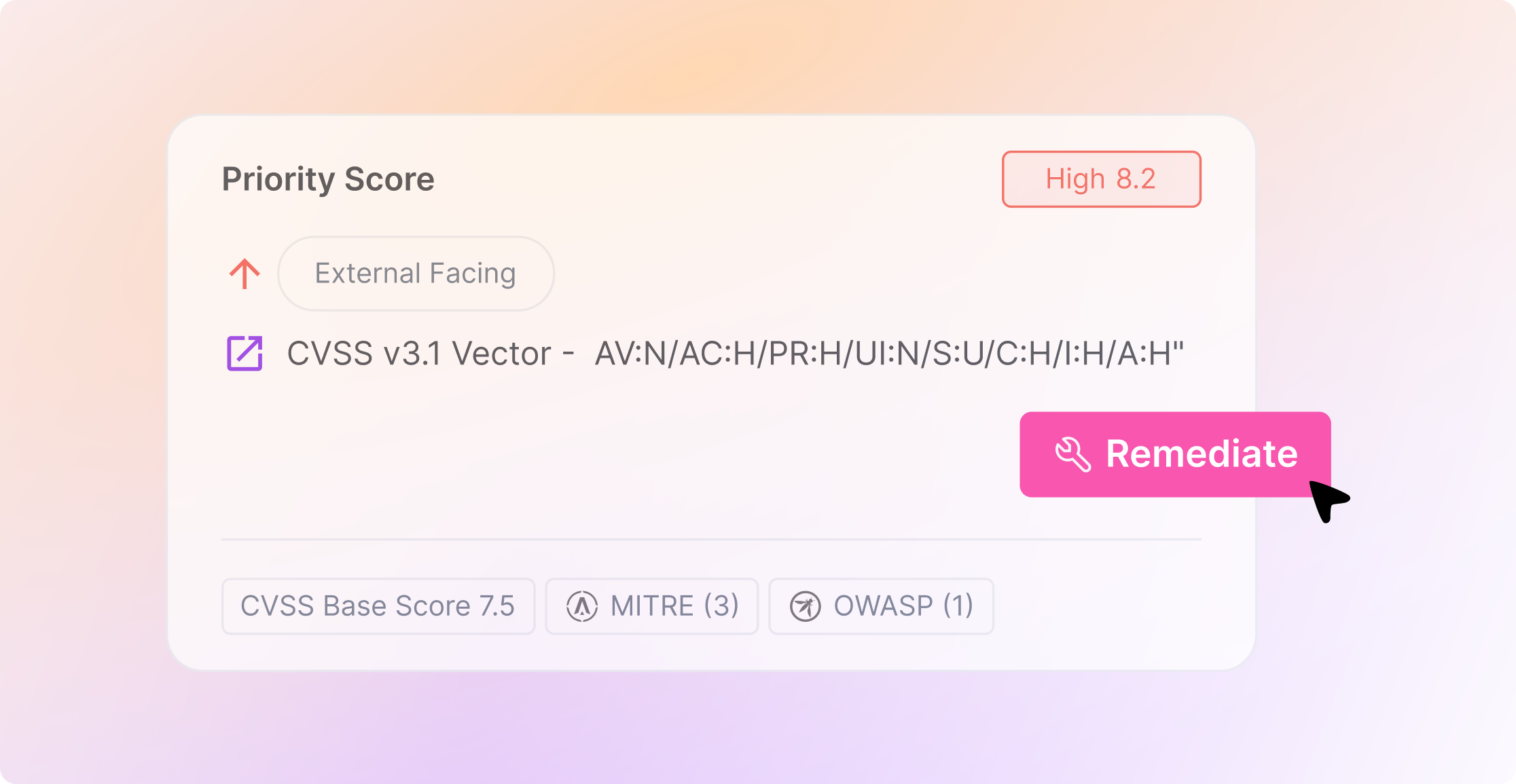
Citizen-built apps and automations often work exactly as intended, until small design choices create large security gaps. Nokod reveals how everyday configurations can quietly introduce exposure.
See What Traditional Tools Can’t
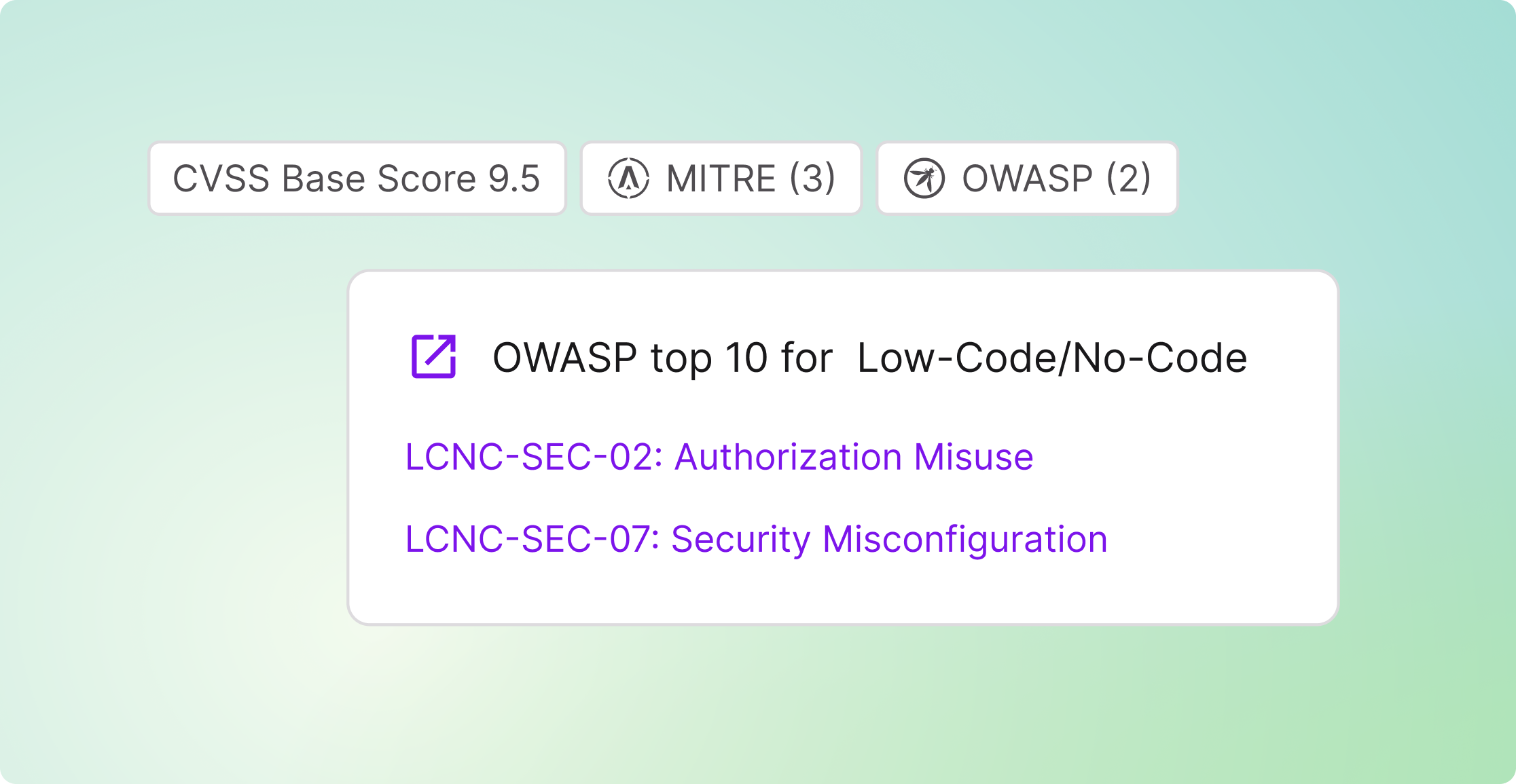
Apps built outside security oversight rarely appear in AppSec dashboards. Nokod discovers and maps no-coders’ assets across platforms, exposing risks aligned with OWASP NCLC security categories, without requiring SAST or DAST.
From zero visibility to a clear map