Supply Chain Security
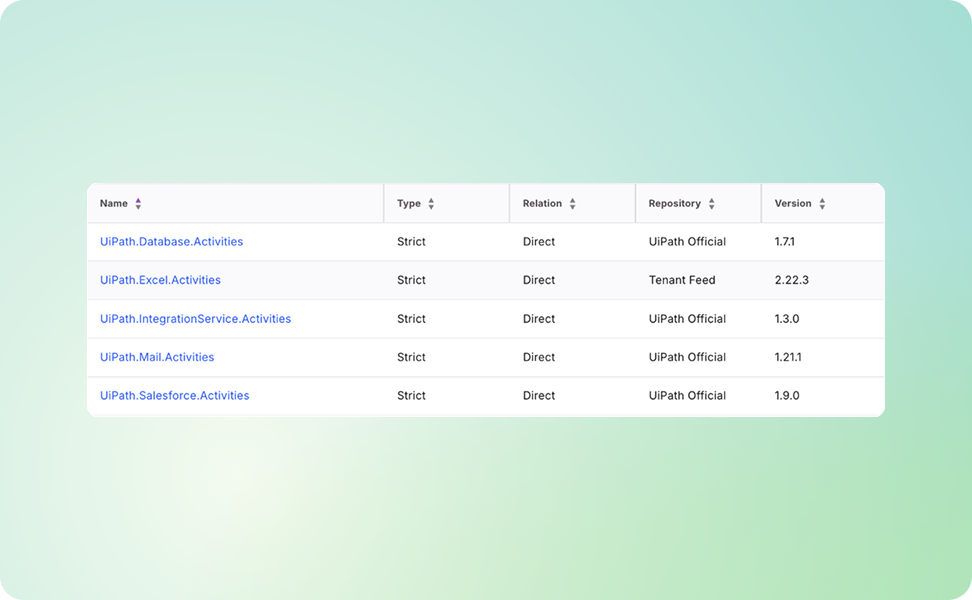
Shadow IT Breeds Hidden Dependencies
Your no-code and automations ecosystems rely on thousands of connectors, APIs, and plugins, many outdated or untrusted.
Nokod brings them into view fast, mapping every dependency in a single day.
When the Roots Get Tangled, Nokod Sorts Them Out
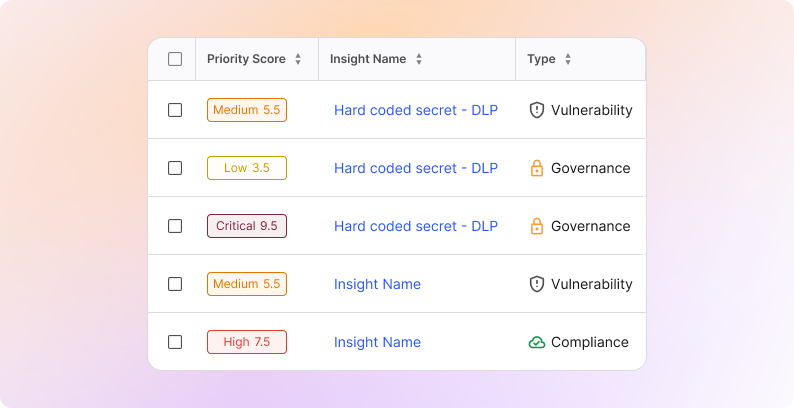
Dependency chains don’t break all at once, they slowly twist. As permissions shift and integrations evolve, hidden pathways form that can quietly expose critical systems.
Nokod tracks dependencies across platforms, identifying untrusted or end-of-life components, unsafe connector usage, high-risk links into sensitive systems, and shadow IT dependencies that bypass security review, before they turn into incidents.
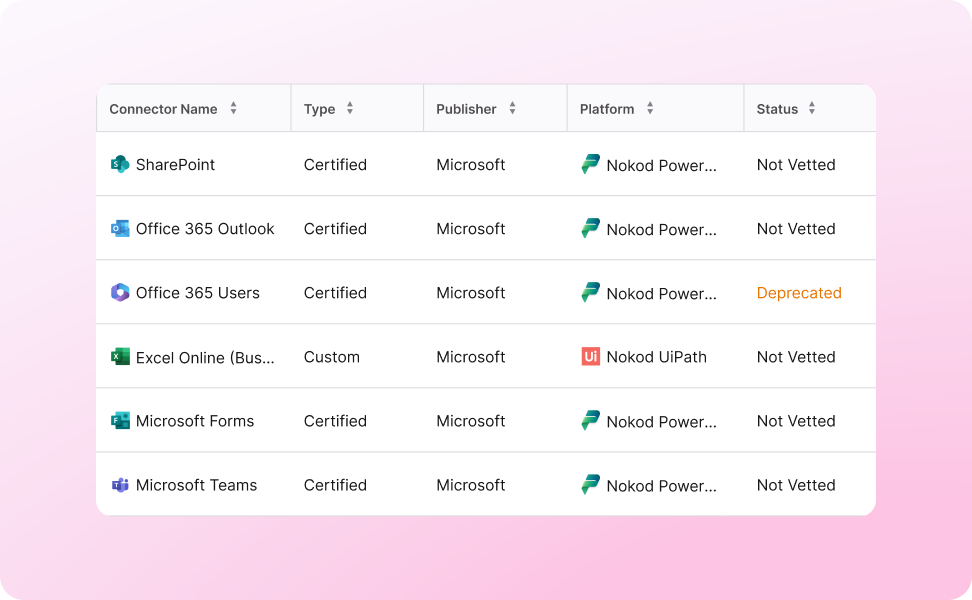
See the Connectors You Didn’t Know Existed
No-code and RPA tools multiply integrations faster than teams can track. Nokod gives you a complete, up-to-date picture of what’s connected and how it’s used.
From blind spots to a clear map
Deprecated or risky connectors still running in production