
The Uncomfortable Truth About Application Security in the Age of No-Coders: Lessons from CVE-2026-20960
It is not uncommon for organizations to detect multiple instances of a new type of vulnerability in their proprietary code. It is also not uncommon for organizations to tackle a newly published vulnerability (CVE) in components used by custom applications.
Over the last decade and a half, enterprises have developed application security practices and tools to handle such events quickly and efficiently.
Imagine their surprise in the face of the recently disclosed CVE-2026-20960, which made them realize that these processes and tools left behind an entire population of thousands of business users, non-professional software developers, who created over the past few years hundreds of thousands of applications.
One CVE, thousands of owners
CVE-2026-20960 is a high-severity (CVSS score 8.0) vulnerability in Microsoft’s Power Apps application. It is a remote code execution vulnerability that can be exploited over the network by authorized users, a term that in many enterprises translates into tens of thousands or hundreds of thousands of individuals (including external contractors).
It also means that any compromise of enterprise credentials immediately translates into a serious breach.
Microsoft patched the cloud-based Power Apps application before disclosing the vulnerability. However, unlike many previous cloud-based vulnerabilities, Microsoft did issue a CVE, which means customers of the application must also take action.
Actually, customers have to take MANY actions.
It turns out that every application created with the vulnerable version of Power Apps needs a simple republishing step to make it safe.
Here is the ugly truth: every one of the thousands of Canvas Apps created by citizen developers needs to be manually published by the same person who created it!
While technically, Microsoft resolved this problem, in a way that should be easy for the “developers” to fix. Operationally, enterprises are facing a risk nightmare.
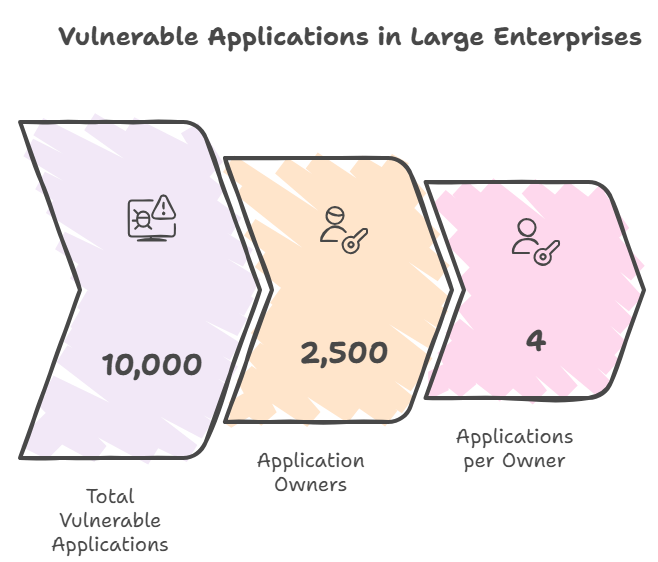
Analysis of some typical environments shows that for medium size environments, there are approximately 700 vulnerable applications that are owned by 200 different individuals. And in large enterprises it rises to around 10,000 vulnerable applications owned by 2,500 individuals.
So while each owner needs to take care of only 4 applications on average, the task of engaging with them all and tracking the progress of the process becomes a daunting one.
What about those poor orphans?
As if chasing the hordes of business users that developed vulnerable applications was not enough, security teams face yet another challenge. In the world of no-coders, applications are being created “on the go” and are never removed, even when their creator (and owner) leaves the organization. As a consequence, many of the Canvas Apps in a typical organization are what security teams refer to as “orphan applications”, applications whose owner is no longer with the organization.
Given that orphan applications are most likely not maintained since the departure of their owner, the chances of these being vulnerable to CVE-2026-20960 are high. In fact we see that up to 30% of vulnerable applications in organizations that we’ve sampled are orphan applications, amounting to 2,300 applications in total, in some cases.
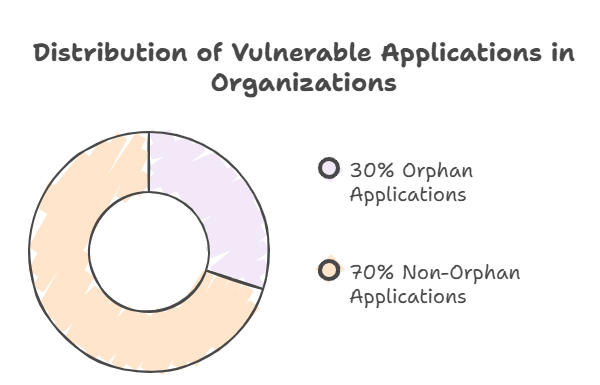
Unlike owner-managed applications, orphaned apps cannot be resolved through notifications or reminders. Remediation requires platform administrators to intervene, reassign ownership, or disable the application entirely. In practice, these apps often persist unnoticed, continuing to access data and integrate with other systems while falling outside regular review cycles. Over time, orphaned vulnerable apps transform what should be temporary exposure into long-term structural risk, remaining exploitable well after patches are released.
Widely Shared Applications and Increased Exploitability
Due to the nature of the vulnerability, risk escalates significantly when vulnerable Canvas Apps are widely shared within the organization.
When analyzing real-world data, we found many vulnerable applications that are accessible to large user groups, departments, or even entire organizations, thereby increasing the potential attack surface available for exploiting CVE-2026-20960. Our analysis shows that 26% of vulnerable applications were shared with 10 or more people and 5% of applications shared with the entire tenant!
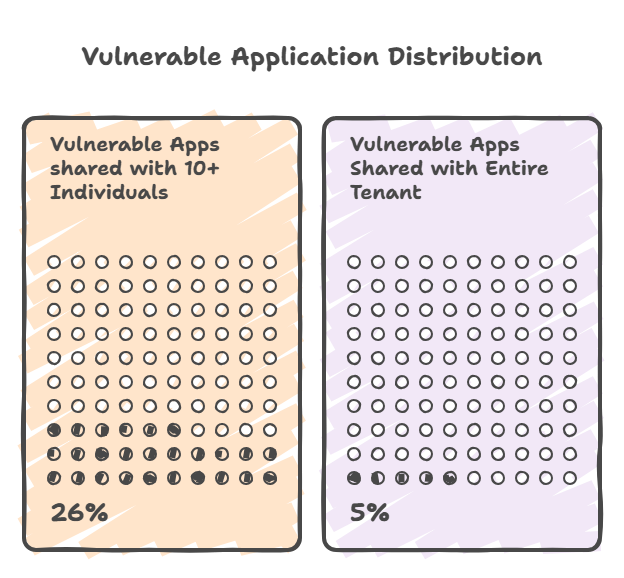
Broad accessibility amplifies severity of this vulnerability, turning application-level vulnerabilities into organization-wide exposure that is difficult to detect and even harder to contain.
Numbers don’t lie
With the complexities involved in the process at high scale, it is no wonder that organizations are struggling with remediation. Our research team found that within two weeks of disclosure, only 6% of vulnerable applications were fixed.
This number increased gradually to only 11% within four weeks of disclosure.
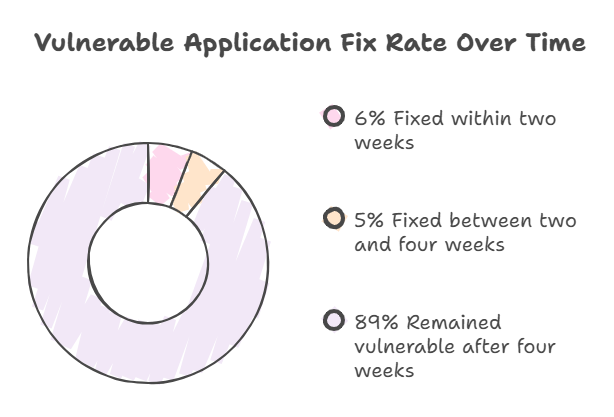
This is not the result of negligence or delayed awareness. It is a consequence of how Power Apps are created, distributed, and maintained at scale. It is the result of not having the right tools and processes required to handle application security at a citizen-developer scale. It is also in part the result of being completely oblivious to the need for application security for these developers.
Such was the surprise to security teams that many of them didn’t even realize that further action was required.
While this issue is unique today, we believe CVE-2026-20960 is an indicator of a broader control gap in citizen-developed environments, where responsibility is unclear, remediation is manual, and exposure persists long after a fix is available.
Getting ready for a new age of application security
Nokod security is already helping organizations get their hands around this new world of application security where ownership is distributed among thousands of non-profession developers across different departments, organizational cultures, locations and languages.
Here are some practical steps you can take to operationalize remediation of CVE-2026-20960 across your Power Platform tenant:
- Identify all vulnerable applications: these were published a Power Apps version earlier than 3.25121 (exact dates differ from tenant to tenant). Power Apps version is available through the Power Platform applications API. A close estimate can be achieved by looking at all applications that were not published after December 1st, 2025.
- Cross reference application owners with your Azure Entra ID records to identify orphan applications. These should be sent out to the platform management team for handling.
- Prioritize applications that are in an active state (not quarantined)
- Look for those applications that are shared to all tenant users (that is a special sharing indication). Prioritize handling of these applications.
- Start sending bulk emails to owners of vulnerable applications by groups that make sense organizationally. Start with those that are geographically closer to you as it will be easier to get their feedback and digest it before working your way through the more remote areas of your organization
The Nokod Security platform automates most of the processes described above for our customers, handling environments with tens of thousands of Canvas Apps.

